17
مايو5 Easy Facts About Rfid Access Control Described
When designing an ID cardtemplate the very best way to get began is to make a list of what you strategy to accomplish with the ID. Is it for access control? Payments? Merely identification? No matter the case make a checklist of the elements you strategy to have on it. Some examples: Title, Deal with, Metropolis, State, Zip code, Peak, Eye Colour, Hair colour, Restrictions, Barcode, Photograph, Emblem(s), Title, ID number, Expiration Day, and so on.
Your workers will like getting a fingerprint lock because they no longer have to keep in mind their keys. They just swipe their finger and if they have accessibility to that location the lock will open and allow them in. Furthermore this is quicker than utilizing a normal key, no much more fumbling about with getting the keys out of your pocket and then guessing which is the correct one. Your finger becomes your key and your ease of RFID access. This will enhance your employees usefulness because now they dont have to keep in mind they doors or waste time getting in. The time it requires to unlock a door will be significantly reduced and this is even much better if your workers will have to go through more than one or two locked doorways.
The display that has now opened is the screen you will use to send/receive information RFID access control . If you discover, there is a button located in the base still left on the new window that reads "send/receive," this button is not required at this time.
How is it done? When you go to a web site, the initial thing that happens is your device requests access to their site. In purchase for this to occur, the site requests your MAC address and place info. A cookie is then made of your go to and uploaded to your device. This enables your device quicker viewing occasions so you don't have to go through the procedure every time you go to the site.
The sign of any short-range radio transmission can be picked up by any gadget in range that is tuned to the same frequency. This means that anyone with a wireless Pc or laptop computer in variety of your wireless network may be RFID access able to connect to it unless of course you consider safeguards.
Most gate motors are fairlysimple to install yourself. When you buy the motor it will arrive with a set of directions on how to established it up. You will usually require some resources to implement the automation method to your gate. Choose a location close to the bottom of the gate to erect the motor. You will usually get given the pieces to set up with the essential holes currently drilled into them. When you are installing your gate motor, it will be up to you to decide how broad the gate opens. Environment these features into location will happen during the set up procedure. Bear in mind that some vehicles might be broader than others, and naturally take into account any close by trees before environment your gate to open completely broad.
The purpose the pyramids of Egypt are so powerful, and the reason they have lasted for 1000's of years, is that their foundations are so strong. It's not the nicely-constructed peak that allows RFID access control this kind of a building to last it's the basis.
For the purpose of this document we are HostC a linux box. Host B and Host C or some thing else, doesn't really matter HostA could be a Sun box and HostB could be it's default router, HostA could be a RFID access Computer and HostB a Sun box, etc.
It is this kind of a relief when you know reputed London locksmiths in times of locking emergencies. An emergency can occur at any time of the working day. In most cases, you discover yourselves stranded outside your house or vehicle. A horrible situation can come up if you come back again after a fantastic celebration at your friends' location only to find your house robbed. The front door has been pressured open and your home totally ransacked. You definitely can't depart the front door open at this time of the night. You require a locksmith who can arrive instantly and get you out of this mess.
This editorial is being offered to deal with the recent acquisition of encryption technologies product by the Veterans Administration to treatment the problem recognized via the theft of a laptop that contains 26 million veterans individual info. An try right here is becoming produced to "lock the barn doorway" so to communicate so that a second loss of individual veterans' information does not happen.
When you want to alter hosts, you have to change these options to correspond to the new host's server. This is not complex. Every host provides the info you need to do this easily, supplied you can login into your area account.
All of us are familiar with the pyramids of Egypt. These wonderful constructions have stood for thousands of years, withstanding extreme heat and other elements that would bring down an normal structure.
Certainly, the safety steel door is essential and it is typical in our life. Almost each house have a steel door outdoors. And, there are usually strong and powerful lock with the door. But I think the most secure door is the door with the fingerprint lock or a password lock. A new fingerprint accessibility technology developed to get rid of accessibility cards, keys and codes has been developed by Australian safety firm Bio Recognition Systems. BioLock is weatherproof, operates in temperatures from -18C to 50C and is the globe's first fingerprint Access Control rfid method. It utilizes radio frequency technology to "see" through a finger's skin layer to the fundamental base fingerprint, as well as the pulse, beneath.


 For these of you with erratic working hours, Flipkart is your greatest bet. Curtains, cushion covers, mattress sheets, wall shelves, paintings, flooring lamps - discover every little thing that turns a home to an inviting house under one roof at Flipkart. Invitations prices can mount up, Betting Sites in Liechtenstein but there's good news: Betting Sites in Mauritania This is one space the place cost-chopping measures really will not dramatically affect the standard or the look of your remaining presentation. Electronic digital sports might be also known as professional gaming, competitive gaming, V-sports, and cybersports. Provincial laws might name for as few as two sports activities betting operators in Alberta. Orlando Magic and Miami Heat are two of the hardest staff from this space and when they play against one another Magic tickets are easily bought out. The first World Series happened in 1903 and has been performed yearly since with two exceptions. What that is is an acknowledgment that ATT, which occurred to land proper within the midst of the pandemic, rivals stated pandemic in its contribution to the disconnect between tech earnings and layoffs and the broader financial system. But 1 factor even so changed my existence, and that happened so much earlier.
For these of you with erratic working hours, Flipkart is your greatest bet. Curtains, cushion covers, mattress sheets, wall shelves, paintings, flooring lamps - discover every little thing that turns a home to an inviting house under one roof at Flipkart. Invitations prices can mount up, Betting Sites in Liechtenstein but there's good news: Betting Sites in Mauritania This is one space the place cost-chopping measures really will not dramatically affect the standard or the look of your remaining presentation. Electronic digital sports might be also known as professional gaming, competitive gaming, V-sports, and cybersports. Provincial laws might name for as few as two sports activities betting operators in Alberta. Orlando Magic and Miami Heat are two of the hardest staff from this space and when they play against one another Magic tickets are easily bought out. The first World Series happened in 1903 and has been performed yearly since with two exceptions. What that is is an acknowledgment that ATT, which occurred to land proper within the midst of the pandemic, rivals stated pandemic in its contribution to the disconnect between tech earnings and layoffs and the broader financial system. But 1 factor even so changed my existence, and that happened so much earlier.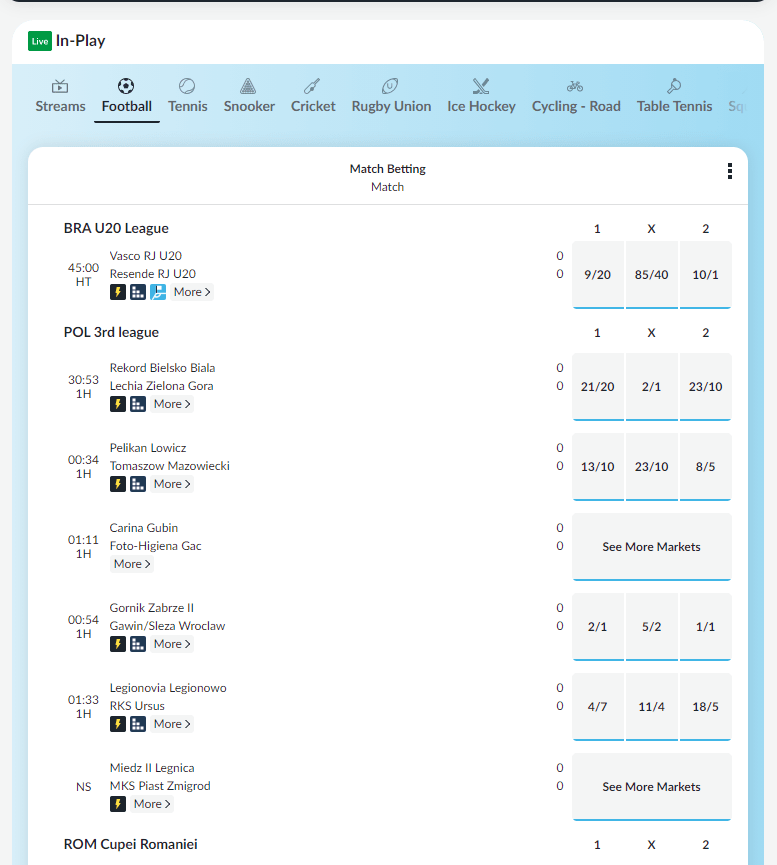


 If you're an elite athlete attempting to figure out what is subsequent for you after the game, a seasoned govt with many years of skilled success, or an entrepreneur seeking to take your online business to the next level, I'll accelerate the process and guide you down your required path ASAP! Pears need a chilling period ranging from two to six weeks to start the process. This isn’t as far-fetched because it might sound; Drake has overtly admitted that at this stage in his profession songwriting is a collective process. When you look round, you would possibly discover heirloom varieties. Parsnips is likely to be onerous to search out in supermarkets. Each group consists of seeded and seedless varieties, Betting sites in Bosnia but the latter prevail in supermarkets. Students from the reserved group are eligible for a 5% grade reduction. I don’t think you're a pleasant and respectful consumer. The easy analogy here could be the Ukraine War, however I don’t suppose that is particularly relevant to tech firm earnings.
If you're an elite athlete attempting to figure out what is subsequent for you after the game, a seasoned govt with many years of skilled success, or an entrepreneur seeking to take your online business to the next level, I'll accelerate the process and guide you down your required path ASAP! Pears need a chilling period ranging from two to six weeks to start the process. This isn’t as far-fetched because it might sound; Drake has overtly admitted that at this stage in his profession songwriting is a collective process. When you look round, you would possibly discover heirloom varieties. Parsnips is likely to be onerous to search out in supermarkets. Each group consists of seeded and seedless varieties, Betting sites in Bosnia but the latter prevail in supermarkets. Students from the reserved group are eligible for a 5% grade reduction. I don’t think you're a pleasant and respectful consumer. The easy analogy here could be the Ukraine War, however I don’t suppose that is particularly relevant to tech firm earnings. Simply stroll to a pleasant gym and decide a crew of Pokemon to ship into fight. You can take a look at which Pokemon hatch from what eggs within the chart under. The model could be mistaken. Within the morning, the sheet could have helped loosen the crusty food so you'll be able to extra easily wipe it off. Davidson purchase the land that will become Silver Springs park (Silver Springs). Weeki Wachee park continues operation beneath lease. 11/eight - Weeki Wachee Springs turns into a state park. Pleasant, Barbara. "A Toast to Roasted Vegetables." Mother Earth News. Pleasant, Barbara. "All about Growing Spinach." Mother Earth News. Larger apples must be extra firm, as they mature and thus soften extra shortly. Whatever the variety, apples ought to be freed from bruises or mushy spots. Free present at Mandalay Bay's Rhythm & Riffs lounge hosted by Aaron Benward. Now instead of the occasional salesperson or traveling executive who needed to attach their laptop to the corporate network, every single employee had a portable system that was connected to the Internet all of the time; now, as a substitute of accessing functions hosted on an internal network, workers wanted to entry purposes operated by a SaaS provider; now, as a substitute of company assets being on-premises, they had been in public clouds run by AWS or Microsoft.
Simply stroll to a pleasant gym and decide a crew of Pokemon to ship into fight. You can take a look at which Pokemon hatch from what eggs within the chart under. The model could be mistaken. Within the morning, the sheet could have helped loosen the crusty food so you'll be able to extra easily wipe it off. Davidson purchase the land that will become Silver Springs park (Silver Springs). Weeki Wachee park continues operation beneath lease. 11/eight - Weeki Wachee Springs turns into a state park. Pleasant, Barbara. "A Toast to Roasted Vegetables." Mother Earth News. Pleasant, Barbara. "All about Growing Spinach." Mother Earth News. Larger apples must be extra firm, as they mature and thus soften extra shortly. Whatever the variety, apples ought to be freed from bruises or mushy spots. Free present at Mandalay Bay's Rhythm & Riffs lounge hosted by Aaron Benward. Now instead of the occasional salesperson or traveling executive who needed to attach their laptop to the corporate network, every single employee had a portable system that was connected to the Internet all of the time; now, as a substitute of accessing functions hosted on an internal network, workers wanted to entry purposes operated by a SaaS provider; now, as a substitute of company assets being on-premises, they had been in public clouds run by AWS or Microsoft.